
The-K 예다함 상조 알아보고 가입까지 : 네이버 블로그

Lead service line identification: A review of strategies and
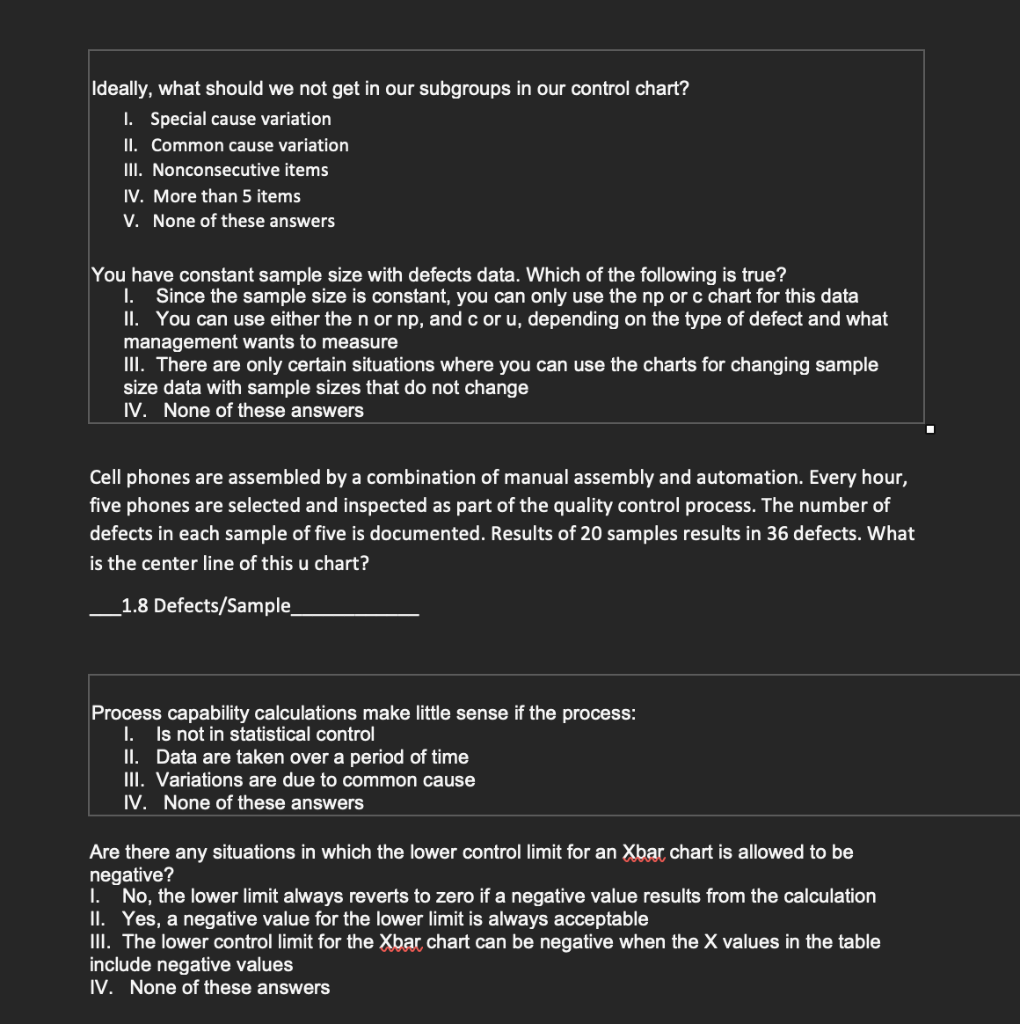
Solved Which of these control chart types allows

··· 게시글 프린트 화면 보기 ···

China: Is peak coal part of its problem?
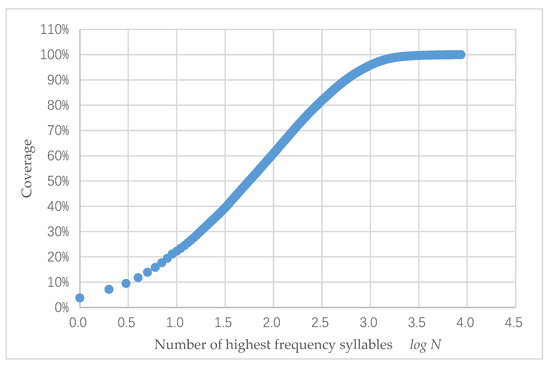
Information, Free Full-Text
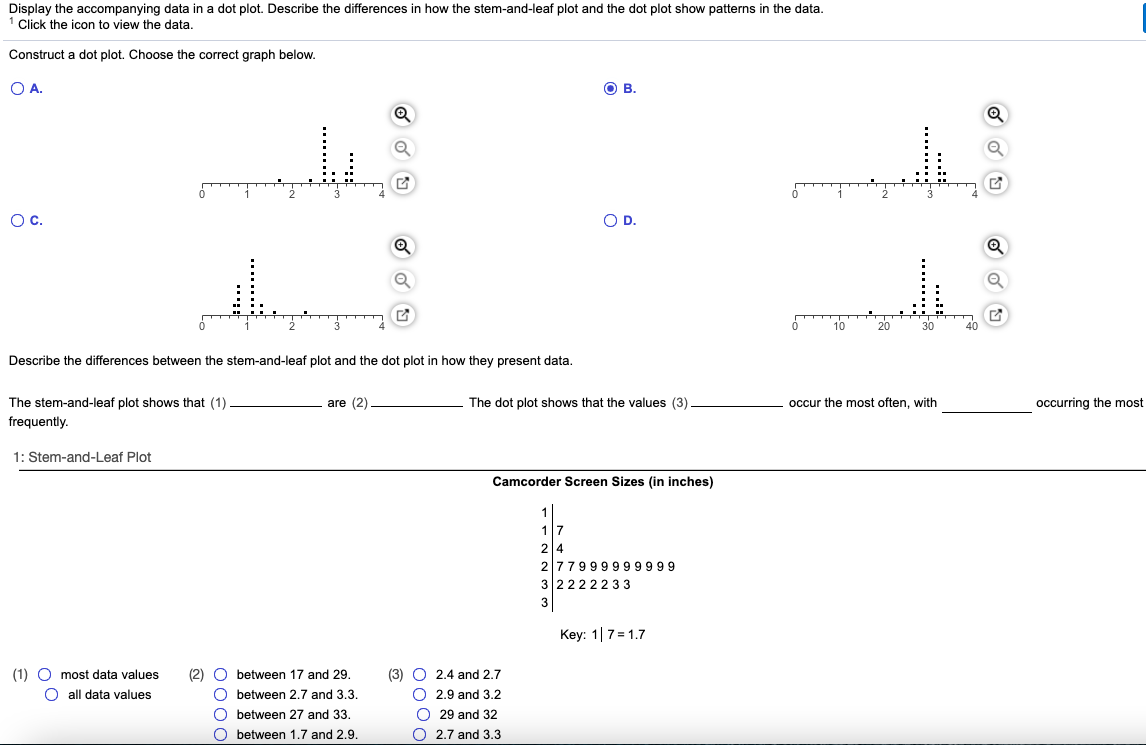
Solved Display the accompanying data in a dot plot. Describe

Calaméo - Creswel L Qualitative Inquiry And Research
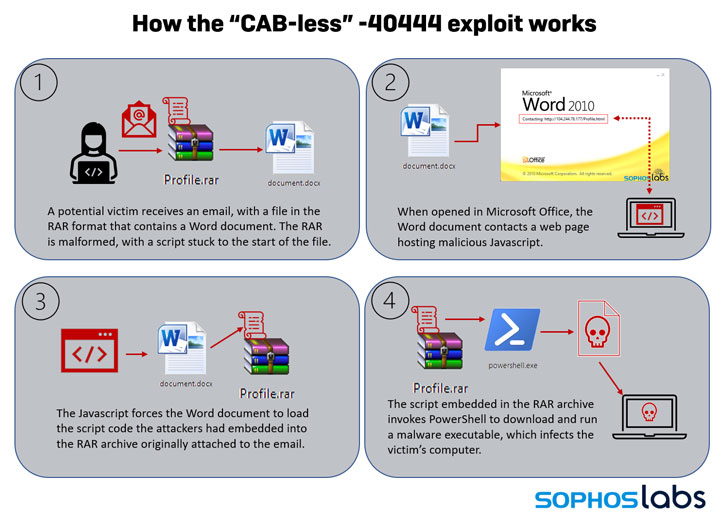
New Exploit Lets Malware Attackers Bypass Patch for Critical
sample_code_2016/scrape_insert_wordpress
Watson
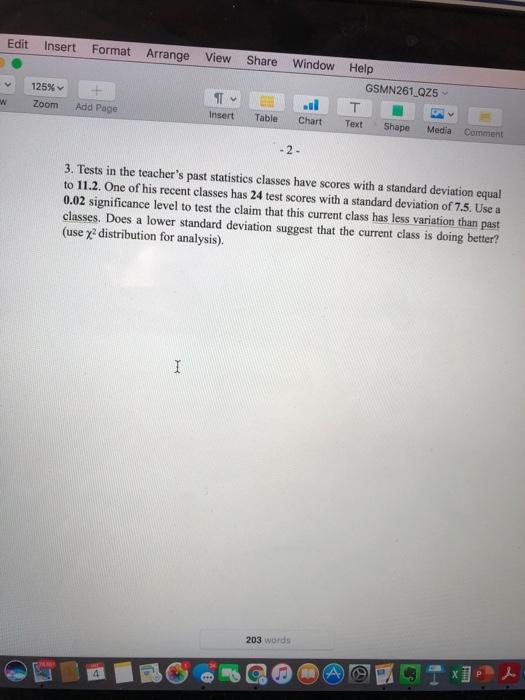
Solved Edit Insert Format Arrange View Share Window Help
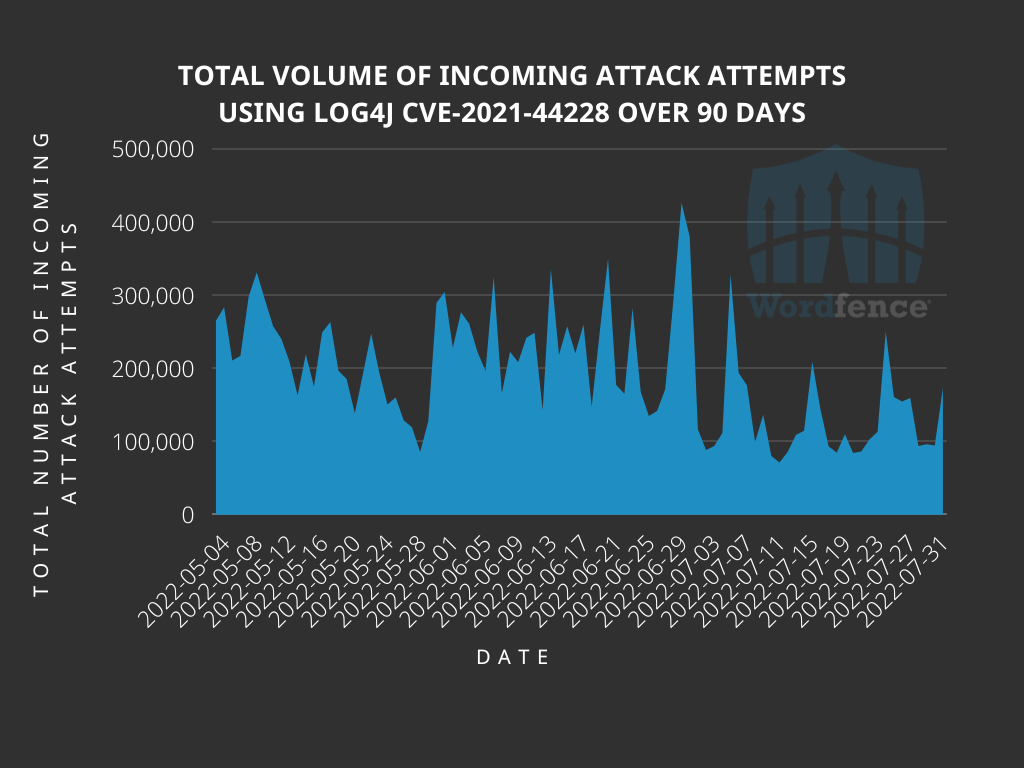
Analyzing Attack Data and Trends Targeting Log4J - vulnerability
